Can Strcpy cause buffer overflow?

Noah Mitchell
Published Jan 10, 2026
The strcpy() function does not stop until it sees a zero (a number zero, '<0') in the source string. Since the source string is longer than 12 bytes, strcpy() will overwrite some portion of the stack above the buffer. This is called buffer overflow.
Is strcpy vulnerable to buffer overflow?
Because strcpy() does not check boundaries, buffer overflow will occur. If this program is running as a set-root-uid program, a normal user can exploit this buffer overflow vulnerability and take over the root privileges.
What is the most common cause of buffer overflow?
Coding errors are typically the cause of buffer overflow. Common application development mistakes that can lead to buffer overflow include failing to allocate large enough buffers and neglecting to check for overflow problems.
What conditions cause buffer overflow?
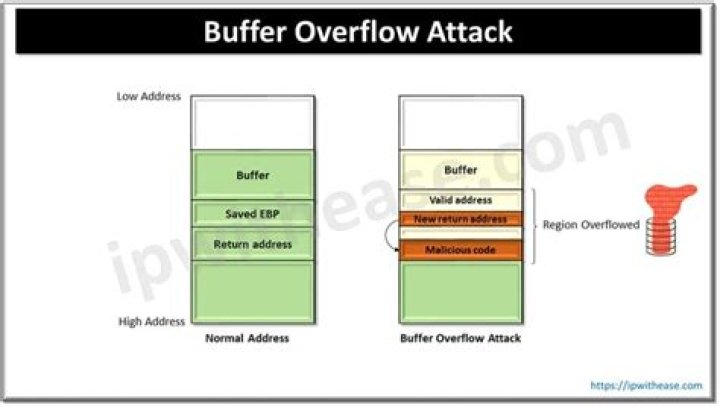
A buffer overflow occurs when data written to a buffer also corrupts data values in memory addresses adjacent to the destination buffer due to insufficient bounds checking. This can occur when copying data from one buffer to another without first checking that the data fits within the destination buffer.
What are the two ways to prevent buffer overflow attacks?
You can prevent a buffer overflow attack by auditing code, providing training, using compiler tools, using safe functions, patching web and application servers, and scanning applications.
42 related questions foundWhat causes heap overflow?
A heap overflow is a form of buffer overflow; it happens when a chunk of memory is allocated to the heap and data is written to this memory without any bound checking being done on the data.
What causes a buffer overflow CCNA?
Explanation: By sending too much data to a specific area of memory, adjacent memory locations are overwritten, which causes a security issue because the program in the overwritten memory location is affected.
What are the most common buffer flow attacks?
What are the different types of buffer overflow attacks?
- Stack overflow attack - This is the most common type of buffer overflow attack and involves overflowing a buffer on the call stack*.
- Heap overflow attack - This type of attack targets data in the open memory pool known as the heap*.
How common are buffer overflow attacks?
According to MITRE, buffer overflows account for over 10,000 of the known software vulnerabilities, 23% of which are considered severe.
Which of the following is the most likely to mitigate against buffer overflow attacks?
Which of the following is the most likely to mitigate against buffer overflow attacks? D. Buffer overflow attacks can often be mitigated by ensuring that you keep up-to-date with system and application patches. As the vendor finds the vulnerabilities, that vendor will fix the issues through a patch.
What is the common cause of buffer over flows cross site scripting SQL injection and format string attacks?
The combination of memory manipulation and mistaken assumptions about the size or makeup of a piece of data is the root cause of most buffer overflows. In this case, an improperly constructed format string causes the program to write beyond the bounds of allocated memory.
What type of operations most likely lead to buffer overflows select one?
Integer overflow attack - When an integer overflows, an arithmetic operation results in an integer (integer) that is too large to store the integer type; this may result in a buffer overflow.
What are some of the C functions susceptible to buffer overflow?
That is why the safest basic method in C is to avoid the following five unsafe functions that can lead to a buffer overflow vulnerability: printf , sprintf , strcat , strcpy , and gets . Unfortunately, the base C language provides only one safe alternative: fgets (to be used instead of gets ).
Which C function can cause buffer overflow and why?
That is why the safest basic method in C is to avoid the following five unsafe functions that can lead to a buffer overflow vulnerability: printf , sprintf , strcat , strcpy , and gets . Unfortunately, the base C language provides only one safe alternative: fgets (to be used instead of gets ).
Is Scanf vulnerable to buffer overflow?
No matter how large the buffer is, there will always be a longer word. Therefore, programs relying on %s are vulnerable to buffer overflows.
What can I use instead of strcpy?
The strncpy() and strncat() functions are similar to the strcpy() and strcat() functions, but each has an additional size_t parameter n that limits the number of characters to be copied. These functions can be thought of as truncating copy and concatenation functions.
What file types are prone to buffer overflows?
A buffer overflow program in Assembly, C, C++ or Fortran is also particularly vulnerable and more likely to enable attackers to compromise a system. However, applications written in JavaScript or Perl are typically less vulnerable to buffer overflow attacks.
Are buffer overflows common?
Most software developers know what a buffer overflow vulnerability is, but buffer overflow attacks against both legacy and newly-developed applications are still quite common.
What causes a buffer overflow quizlet?
A stack buffer overflow occurs when the targeted buffer is located on the stack, usually as a local variable in a function's stack frame. The exploits include an unchecked buffer overflow resulting from the use of the C gets() function.
Can buffer overflow happen in heap?
A heap overflow condition is a buffer overflow, where the buffer that can be overwritten is allocated in the heap portion of memory, generally meaning that the buffer was allocated using a routine such as malloc().
What are different buffer overflow attacks?
There are two types of buffer overflows: stack-based and heap-based. Heap-based, which are difficult to execute and the least common of the two, attack an application by flooding the memory space reserved for a program.
How many primary ways are there for detecting buffer overflow?
How many primary ways are there for detecting buffer-overflow? Explanation: There are two ways to detect buffer-overflow in an application.
How does a buffer overflow work?
A buffer overflow occurs when a program or process attempts to write more data to a fixed length block of memory (a buffer), than the buffer is allocated to hold. By sending carefully crafted input to an application, an attacker can cause the application to execute arbitrary code, possibly taking over the machine.
How do you mitigate ping sweeps?
What method can be used to mitigate ping sweeps?
- using encrypted or hashed authentication protocols.
- installing antivirus software on hosts.
- deploying antisniffer software on all network devices.
- blocking ICMP echo and echo-replies at the network edge.
Which of the following can cause stack overflow?
The most-common cause of stack overflow is excessively deep or infinite recursion, in which a function calls itself so many times that the space needed to store the variables and information associated with each call is more than can fit on the stack.



