How do you categorize information systems?

Emily Sparks
Published Jan 25, 2026
The process for categorizing information and data consists of determining the potential impact, LOW (L), MODERATE (M), or HIGH (H), to the Confidentiality (C), Integrity (I) and Availability (A) of the information and data.
Why is it important to categorize information systems?
ecurity categorization standards for information and systems provide a common framework and understanding for expressing security impacts that promotes: (i) effective risk management and oversight of systems and (ii) consistent reporting to the Office of Management and Budget (OMB) and Congress.
How do we categorize?
Categorization is the process through which ideas and objects are recognized, differentiated, classified, and understood. The word “categorization” implies that objects are sorted into categories, usually for some specific purpose. This process is vital to cognition.
Who is primarily responsible for categorizing the information system?
3. WHO IS RESPONSIBLE FOR CATEGORIZING EACH INFORMATION SYSTEM? Organizations should conduct security categorizations as an organization-wide activity with the involvement of the senior leadership and other key officials within the organization.
What is RMF categorization?
Standard for categorizing information and systems according to an organization's level of concern for confidentiality, integrity, and availability and the potential impact on organizational assets and operations.
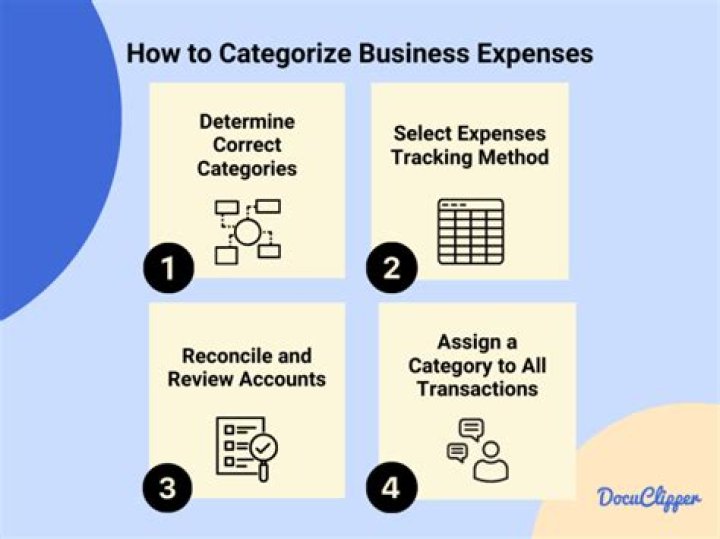
27 related questions foundWhat is the first step in the categorization process?
d. The first step in categorizing information is to create the categories.
What must be categorized first in the RMF Step 1 security categorization process?
In preparing for the first step of the RMF Process, Categorization, the Mission/Business Owner/Information System Owner is responsible for identifying all information types.
What is a system categorization?
Information and Information System Data Categorization Processes. The general process for categorizing information and research data, categorizing information systems, and protecting the information and data pursuant to the policy is as follows: Categorize the institutional information and research data.
What is categorization in cyber security?
Definition(s): The process of determining the security category for information or an information system. Security categorization methodologies are described in CNSS Instruction 1253 for national security systems and in FIPS 199 for other than national security systems.
What are the three factors in system categorization of the cyber security risk management framework?
Risk Management Framework (RMF) Objectives
Implementing a three-tiered approach to risk management that addresses risk-related concerns at the enterprise level, the mission and business process level, and the information system level.
What are the three levels of categorization?
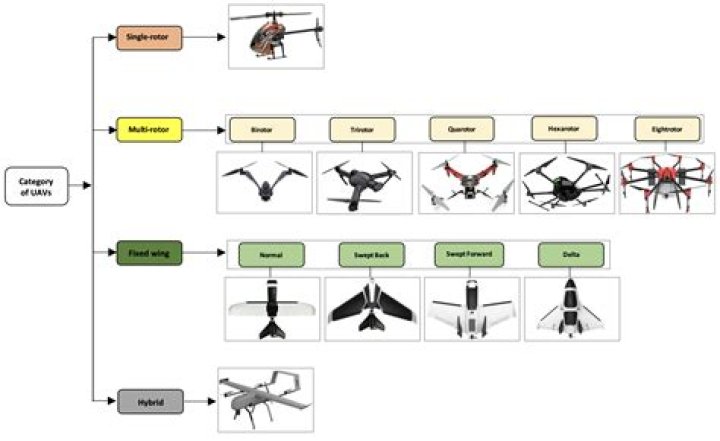
As we can see in figure 1, there are three levels of categorization: basic, superordinate and subordinate.
What is your basis for categorizing?
Categorization is the ability and activity to recognize shared features or similarities between the elements of the experience of the world (such as objects, events, or ideas), organizing and classifying experience by associating them to a more abstract group (that is, a category, class, or type), on the basis of their ...
What makes a category member typical?
a "typical" member in a category. It is based on an average of members of a category that are commonly experienced.
What is the difference between classification and categorization?
Classification involves a formalized, predefined system of organization while categorization is any grouping based on a similarity.
Are information systems unique or general?
General Purpose vs.
DBMS software is typically not designed to work with a specific organization or a specific type of analysis. Rather, it is a general-purpose information system. Another example is an electronic spreadsheet.
When should a new DoD information system be registered?
Under RMF, a new information system may be registered at any time before it is decommissioned. Impact values are assigned based on potential harm to the organization, regardless of potential harm to the nation or individuals. Security control assessment procedures are maintained by each DoD component.
What are the main components of the NIST cybersecurity framework?
NIST framework is divided into 5 main functions. These functions are as follows: identity, protect, detect, respond, and recover. They support an organization in expressing its management of cybersecurity risk by addressing threats and developing by learning from past activities.
What is the NIST RMF?
The NIST Risk Management Framework (RMF) provides a comprehensive, flexible, repeatable, and measurable 7-step process that any organization can use to manage information security and privacy risk for organizations and systems and links to a suite of NIST standards and guidelines to support implementation of risk ...
How many types of cyber security are there?
Cybersecurity can be categorized into five distinct types: Critical infrastructure security. Application security. Network security.
How can data categorization aid in mitigating threats?
Data Classification Definition
Data classification helps organizations answer important questions about their data that inform how they mitigate risk and manage data governance policies. It can tell you where you are storing your most important data or what kinds of sensitive data your users create most often.
What publication assists with system categorization?
The National Institute of Standards and Technology (NIST) Special Publication (SP) 800-60 has been developed to assist Federal government agencies to categorize information and information systems.
What is CIA in terms of information security?
The three letters in "CIA triad" stand for Confidentiality, Integrity, and Availability. The CIA triad is a common model that forms the basis for the development of security systems. They are used for finding vulnerabilities and methods for creating solutions.
How do you categorize incidents?
Incidents can be categorized by call, by type, by caller, by technology, by incident, or by service. The first decision is which of these is most important to the customer? Typically, organizations that are implementing service management will take the approach of starting with the service.
Why is categorization important in an operational control environment?
The activity of categorizing the incident speeds up the incident management process and creates greater efficiency within the process flow. If the issue cannot be solved, the categorization determines the appropriate incident escalation group.