How does a ping of death work?

William Rodriguez
Published Jan 18, 2026
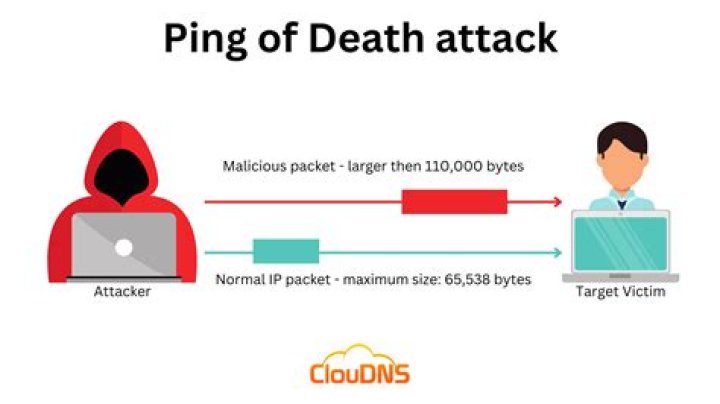
A Ping of death (PoD) attack is a denial-of-service (DoS) attack, in which the attacker aims to disrupt a targeted machine by sending a packet larger than the maximum allowable size, causing the target machine to freeze or crash.
Can you DDoS with ping?
A ping flood is a denial-of-service attack in which the attacker attempts to overwhelm a targeted device with ICMP echo-request packets, causing the target to become inaccessible to normal traffic. When the attack traffic comes from multiple devices, the attack becomes a DDoS or distributed denial-of-service attack.
How does a smurf attack work?
A smurf attack is a form of a DDoS attack that causes packet flood on the victim by exploiting/abusing ICMP protocol. When deployed, large packets are created using a technique called “spoofing”. The phony source address that is now attached to these packets becomes the victim, as their IP is flooded with traffic.
What is ICMP ping of death?
Ping of death is a strategy for DoS (Denial of Service) assault. It's an attack-type that objectifies the ICMP (Internet Control Message Protocol) and the TCP (Transmission Control Protocol, and is quite possibly the most undermining of all ICMP attacks. The ping of death attack is otherwise called a teardrop attack.
How does a DoS attack work?
A Denial-of-Service (DoS) attack is an attack meant to shut down a machine or network, making it inaccessible to its intended users. DoS attacks accomplish this by flooding the target with traffic, or sending it information that triggers a crash.
17 related questions foundHow long can DoS attacks last?
1 This is usually accomplished by flooding the targeted host or network with traffic until the target can't respond or crashes. DoS attacks can last anywhere from a few hours to many months and can cost companies time and money while their resources and services are unavailable.
Who is typically targeted in a DoS attack?
A DoS or DDoS attack is analogous to a group of people crowding the entry door of a shop, making it hard for legitimate customers to enter, thus disrupting trade. Criminal perpetrators of DoS attacks often target sites or services hosted on high-profile web servers such as banks or credit card payment gateways.
Does the ping of death still work?
Does the ping of death still work? Modern computers are protected against ping of death attacks and have been since the late 1990s. However, there are still examples of vulnerabilities that can be exploited by using the ping of death approach.
What kind of vulnerability is exploited by a ping of death?
Ping of death in IPv6
Windows TCP/IP stack did not handle memory allocation correctly when processing incoming malformed ICMPv6 packets, which could cause remote denial of service. This vulnerability was fixed in MS13-065 in August 2013. The CVE-ID for this vulnerability is CVE-2013-3183.
What year did the ping of death first appear?
The ping of death is an attack of the past. Since the attack was discovered in 1997, adjustments were made to server software and operating systems to provide protection against it.
Which technique is used in a Smurf attack?
A Smurf attack is a resource consumption attack using ICMP Echo as the mechanism. ICMP Echo attacks seek to flood the target with ping traffic and use up all available bandwidth.
What is the difference between a Smurf attack and a DDoS attack?
A Smurf attack is a form of a distributed denial of service (DDoS) attack that renders computer networks inoperable. The Smurf program accomplishes this by exploiting vulnerabilities of the Internet Protocol (IP) and Internet Control Message Protocols (ICMP).
Which of the following is true in a Smurf attack?
A Smurf attack scenario can be broken down as follows: Smurf malware is used to generate a fake Echo request containing a spoofed source IP, which is actually the target server address. The request is sent to an intermediate IP broadcast network. The request is transmitted to all of the network hosts on the network.
What is ICMP flooding?
An Internet Control Message Protocol (ICMP) flood DDoS attack, also known as a Ping flood attack, is a common Denial-of-Service (DoS) attack in which an attacker attempts to overwhelm a targeted device with ICMP echo-requests (pings).
What is ICMP spoofing?
ICMP Ping Spoofing Attack
Victim's source IP is spoofed to send a ping to server from Attacker. As the source IP is spoofed server takes is as a original IP and hence ping reply is sent to victim instead of attacker who send the actual ping request.
Can a VPN stop DDoS?
Generally speaking, yes, VPNs can stop DDoS attacks. A primary benefit of a VPN is that it hides IP addresses. With a hidden IP address, DDoS attacks can't locate your network, making it much harder to target you.
What is large ping?
A correctly formed ping message is typically 56 bytes in size, or 84 bytes when the Internet Protocol [IP] header is considered. Historically, many computer systems could not properly handle a ping packet larger than the maximum IPv4 packet size. Larger packets could crash the target computer.
Can pinging a website crash it?
Since the sent data packages are larger than what the server can handle, the server can freeze, reboot, or crash. This type of attack uses large amounts of Internet Control Message Protocol (ICMP) ping traffic target at an Internet Broadcast Address. The reply IP address is spoofed to that of the intended victim.
How does a slow loris work?
Slowloris works by opening multiple connections to the targeted web server and keeping them open as long as possible. It does this by continuously sending partial HTTP requests, none of which are ever completed.
What is the strongest DDoS method?
DNS Flood. One of the most well-known DDoS attacks, this version of UDP flood attack is application specific – DNS servers in this case. It is also one of the toughest DDoS attacks to detect and prevent.
How does a SYN flood work?
In a SYN flood attack, the attacker sends repeated SYN packets to every port on the targeted server, often using a fake IP address. The server, unaware of the attack, receives multiple, apparently legitimate requests to establish communication. It responds to each attempt with a SYN-ACK packet from each open port.
What is it called if a hacker takes down multiple services very quickly with the help of botnets?
What is it called if a hacker takes down multiple services very quickly with the help of botnets? Distributed denial-of-service (DDoS)
What are the consequences to an Organisation of a DoS attack?
Distributed denial of service attacks can cause server outages and monetary loss and place excessive stress on IT professionals trying to bring resources back online. The right detection and prevention methods can help stop a DDoS event before it gains enough momentum to topple company networks.
What are the three basic types of denial of service attacks?
Broadly speaking, DoS and DDoS attacks can be divided into three types:
- Volume Based Attacks. Includes UDP floods, ICMP floods, and other spoofed-packet floods. ...
- Protocol Attacks. Includes SYN floods, fragmented packet attacks, Ping of Death, Smurf DDoS and more. ...
- Application Layer Attacks.
How often do DDoS attacks happen?
According to a SecurityWeek article, “By combining the direct attacks with the reflection attacks, the researchers discovered that the internet suffers an average of 28,700 distinct DoS attacks every day.



